Needing a temporary email address sign up for something online? You might want to consider a throwaway email account. These accounts are designed specifically for temporary situations, like signing up for free trials that you don't wish to keep long-term.
A throwaway email account gives you increased privacy by keeping your main email address from possibly malicious sites and services.
- Throwaway emails are often used for:
- Creating accounts on social media platforms
- Protecting your main email from spam
- Participating in online surveys without revealing your identity
The Veil of Virtual Personhood
In the ever-expanding virtual sphere, individuals often crave a sense of privacy. This desire has birthed the concept of an anonymous online identity, a persona that allows users to explore themselves differently from their real-world counterparts.
The allure of anonymity draws many to construct elaborate online identities, often separate from their true selves. Users may assume alias, fabricate tales, and even alter their digital appearances.
The motivations for adopting an anonymous online identity span a wide range. Some strive to evade societal expectations, while others aim to express themselves freely. Still, others exploit anonymity for criminal activities.
The ethical and societal ramifications of anonymous online identities continue to be debated in the digital age.
Hidden Correspondence Channel
In the labyrinthine world of espionage, a secure communication channel is paramount. A hidden correspondence system acts as the lifeline for clandestine operations, allowing operatives to send vital data while evading detection. This delicate network often involves encrypted messages, aliases, and physical meetups conducted in obscure locations.
- Traditionally , such channels relied on dead drops to transmit messages, but the advent of technology has created new and complex methods.
- Today, virtual networks provide masked platforms for operatives to converse.
- Furthermore, the use of steganography can further obscure the true content of messages.
Keeping a secure correspondence channel is a ongoing challenge, requiring vigilance and adaptation to evolving threats. Any failure in security can have grave consequences for an operation.
Provisional Communication Link
A temporary communication link is established to facilitate contact between two parties when a fixed connection cannot be maintained. These links are often used in critical scenarios where consistent communication is crucial for operation. They can also be implemented in challenging terrains where establishing a standard link is unpractical.
Deployment of a temporary communication link often involves mobile equipment to relay information over limited bandwidths.
Note that the effectiveness of a temporary communication link is contingent upon factors such as environmental conditions and the range check here of the technology used.
An Unexplained Sender's Address
Sometimes, you might receive correspondence with/from/featuring an address that appears to be fabricated/unidentifiable/undetectable. This situation/scenario/circumstance can cause/bring about/lead to a range/variety/selection of concerns/worries/feelings.
It's important/essential/crucial to remember that an unidentified sender's address inherently mean the mail is dangerous/suspicious/harmful. There are several/various/numerous possible explanations, including/such as/like someone making a mistake/typing incorrectly/using a false address.
If you receive/encounter/come across mail with an unidentified sender's address/from an unidentifiable source/featuring an unknown address, it's best to exercise caution/be careful/proceed with care.
An Online Alias
A digital pseudonym is a assumed name or identity used in the digital realm. It serves to enhance privacy, allowing individuals to separate their online and offline lives. Pseudonyms can range from simple usernames to elaborate fictional personas, creating a safe space for interaction and self-exploration.
 Jake Lloyd Then & Now!
Jake Lloyd Then & Now!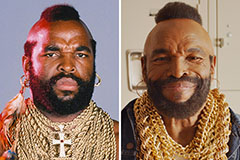 Mr. T Then & Now!
Mr. T Then & Now! Rachael Leigh Cook Then & Now!
Rachael Leigh Cook Then & Now! Catherine Bach Then & Now!
Catherine Bach Then & Now!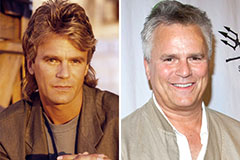 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now!